How Dare They Peep into My Private Life?”: Children's Rights Violations by Governments that Endorsed Online Learning During the Covid-19 Pandemic | HRW
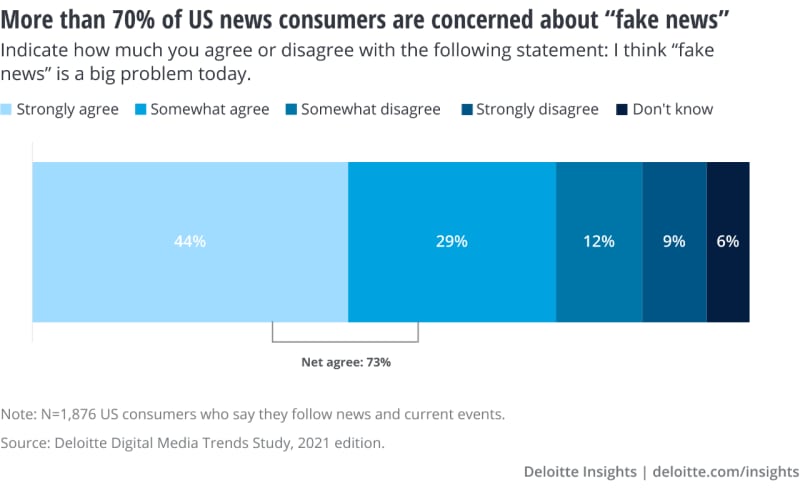
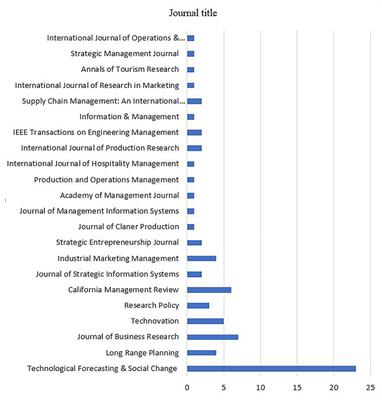
A systematic review on fake news research through the lens of news creation and consumption: Research efforts, challenges, and future directions | PLOS ONE

Visually Hidden, Self-Assembled Porous Polymers for Optical Physically Unclonable Functions | ACS Applied Materials & Interfaces
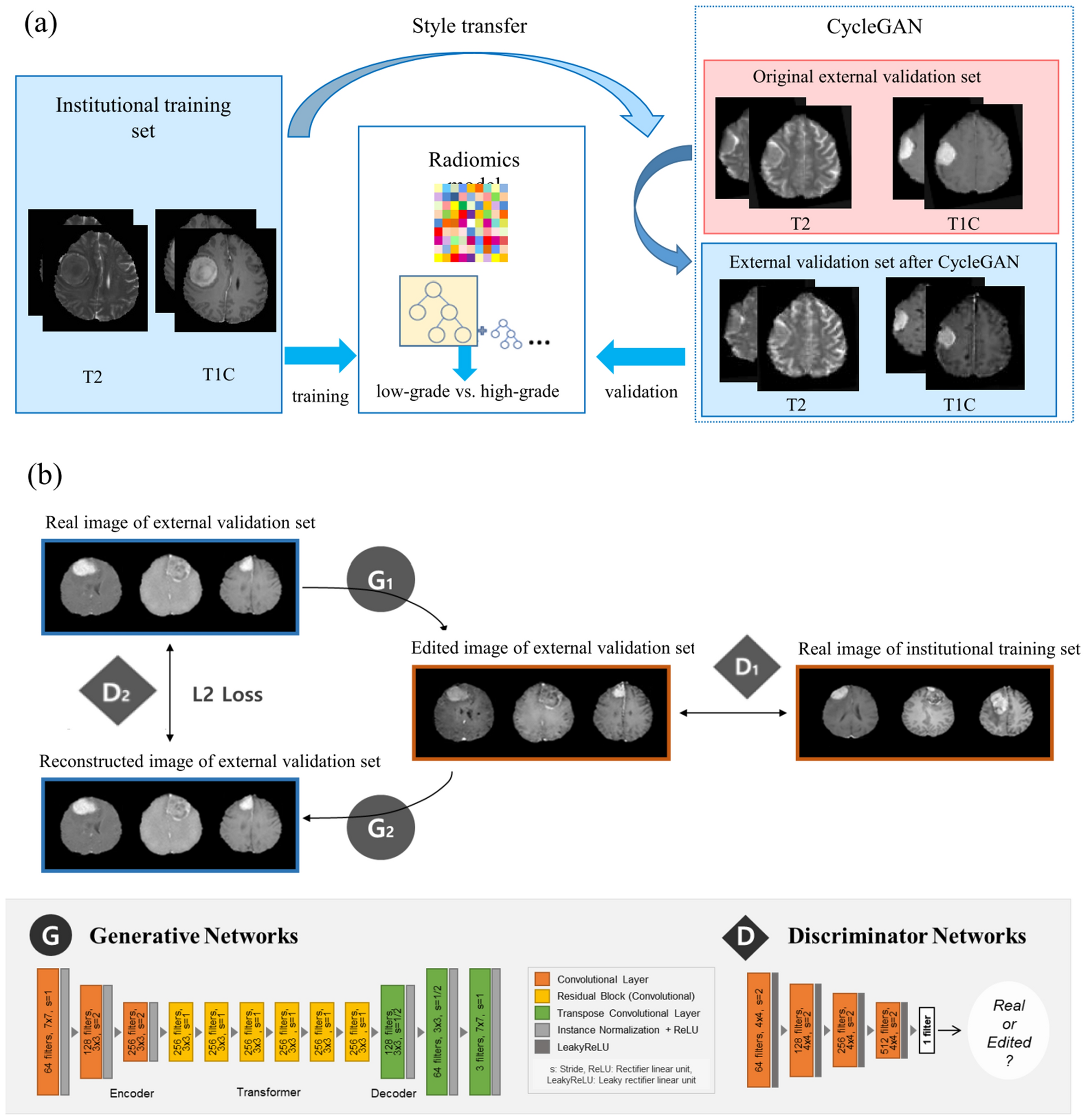
Cycle-consistent adversarial networks improves generalizability of radiomics model in grading meningiomas on external validation | Scientific Reports
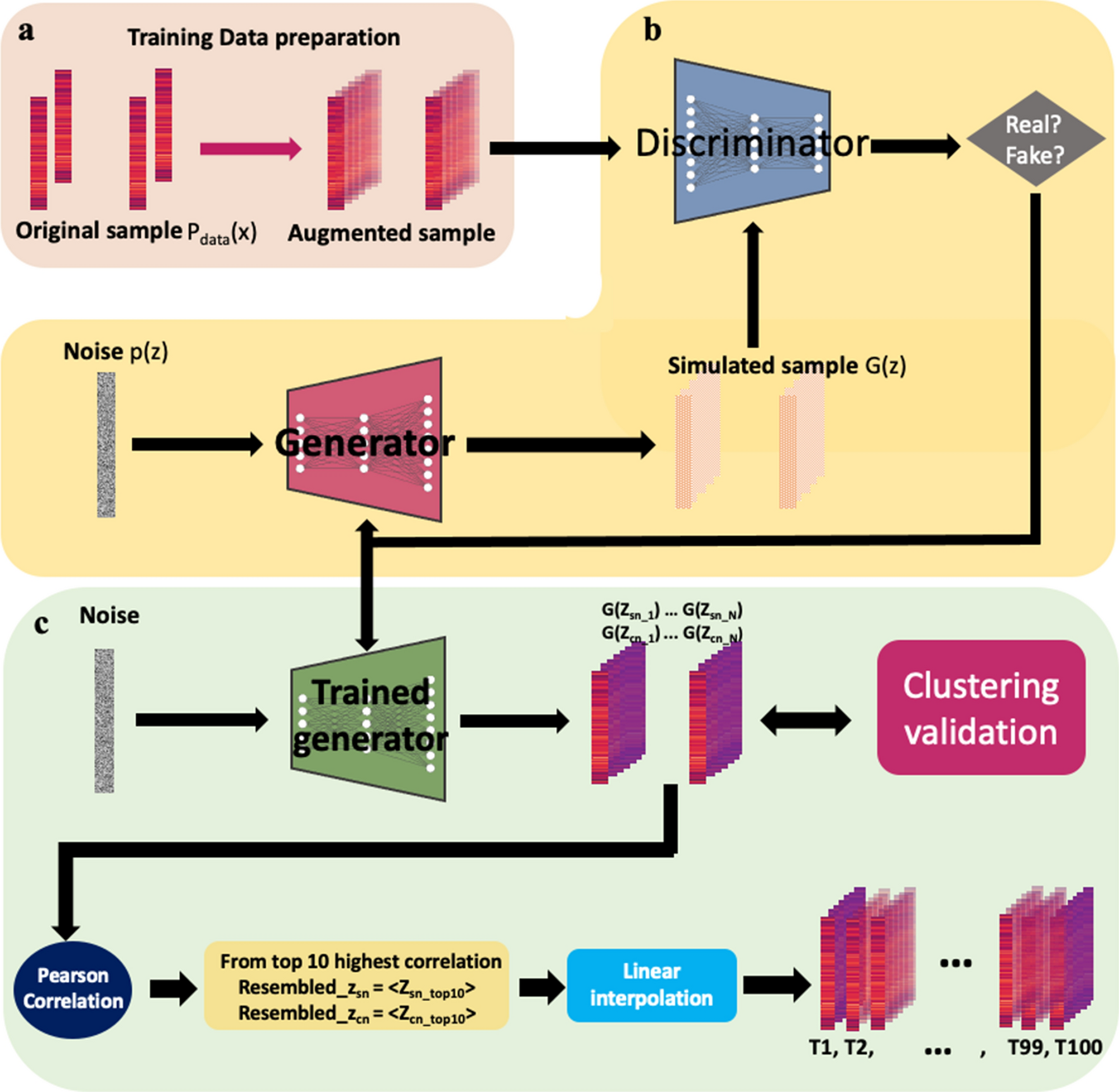
Unveiling OASIS family as a key player in hypoxia–ischemia cases induced by cocaine using generative adversarial networks | Scientific Reports
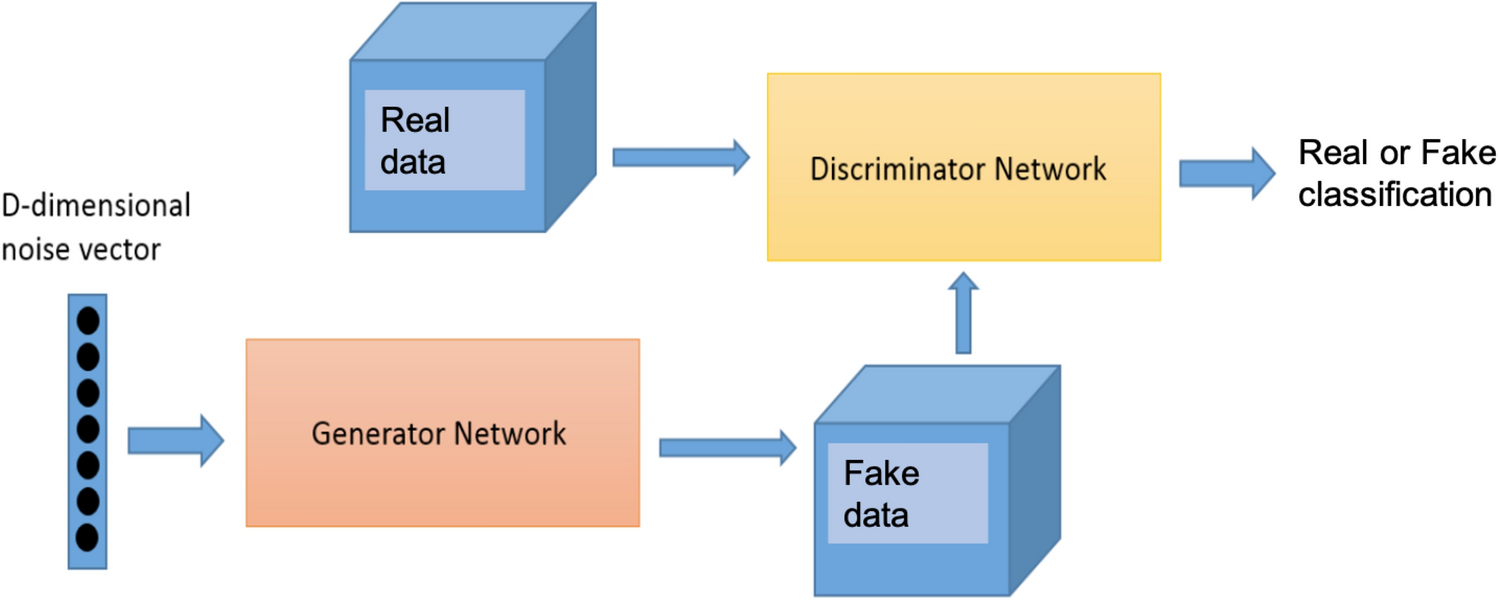
Synthetic flow-based cryptomining attack generation through Generative Adversarial Networks | Scientific Reports

12 The Neglected Mega-Problem: Illicit Trade in “Normally Licit” Goods > PRISM | National Defense University > News

Deep learning model to predict complex stress and strain fields in hierarchical composites | Science Advances

Sensors | Free Full-Text | Conditional Generative Adversarial Networks for Data Augmentation of a Neonatal Image Dataset

Institutional versus commercial email addresses: which one to use in your publications? | Impact of Social Sciences
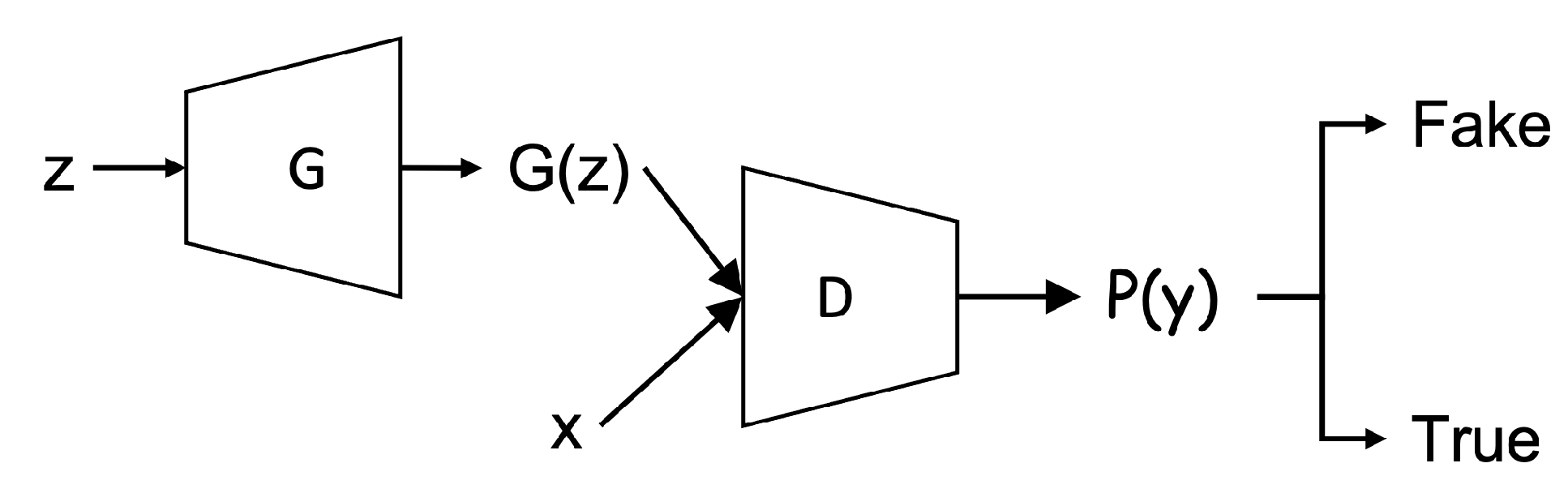
Computers | Free Full-Text | Improved Bidirectional GAN-Based Approach for Network Intrusion Detection Using One-Class Classifier
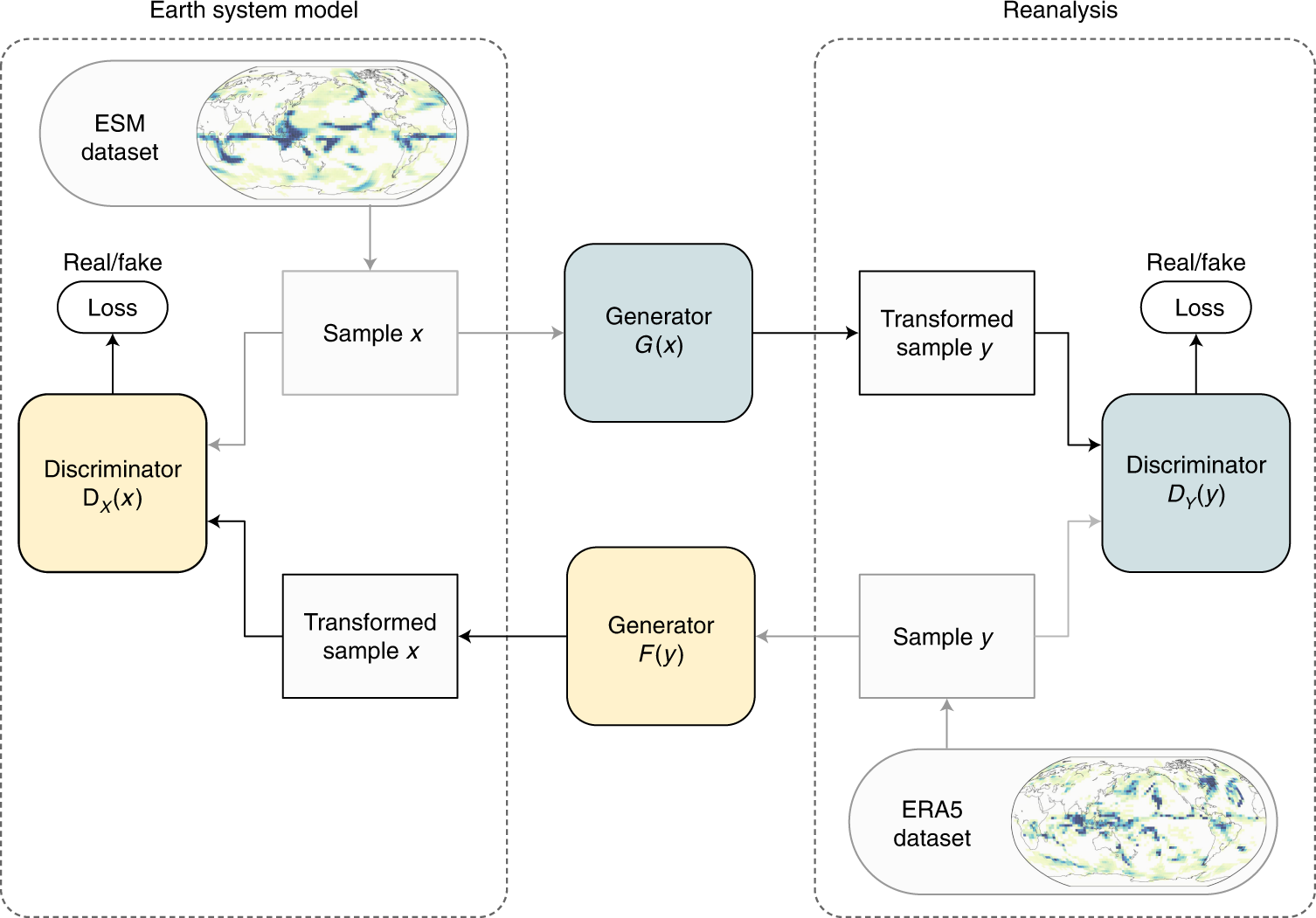
Physically constrained generative adversarial networks for improving precipitation fields from Earth system models | Nature Machine Intelligence